Creating a limited URL provider is a fascinating task that entails various facets of application advancement, which includes Net enhancement, databases administration, and API style and design. Here is an in depth overview of the topic, with a target the crucial components, problems, and greatest techniques linked to creating a URL shortener.
1. Introduction to URL Shortening
URL shortening is a method over the internet wherein a protracted URL might be converted right into a shorter, far more manageable kind. This shortened URL redirects to the initial prolonged URL when frequented. Products and services like Bitly and TinyURL are very well-recognised samples of URL shorteners. The necessity for URL shortening arose with the arrival of social websites platforms like Twitter, where by character limitations for posts built it tricky to share lengthy URLs.
code qr reader
Over and above social media marketing, URL shorteners are handy in advertising strategies, emails, and printed media where extensive URLs is usually cumbersome.
2. Core Elements of the URL Shortener
A URL shortener typically is made of the next components:
Website Interface: This is the entrance-stop aspect exactly where customers can enter their long URLs and receive shortened versions. It could be a simple kind over a Web content.
Databases: A database is important to shop the mapping between the original extensive URL and the shortened version. Databases like MySQL, PostgreSQL, or NoSQL alternatives like MongoDB can be utilized.
Redirection Logic: Here is the backend logic that usually takes the short URL and redirects the user towards the corresponding extended URL. This logic will likely be implemented in the net server or an application layer.
API: Numerous URL shorteners supply an API making sure that third-occasion purposes can programmatically shorten URLs and retrieve the initial extensive URLs.
three. Coming up with the URL Shortening Algorithm
The crux of the URL shortener lies in its algorithm for changing a protracted URL into a short a person. Quite a few techniques may be employed, such as:
eat bulaga qr code registration
Hashing: The long URL is usually hashed into a set-dimensions string, which serves given that the short URL. Having said that, hash collisions (unique URLs leading to exactly the same hash) must be managed.
Base62 Encoding: One particular typical solution is to utilize Base62 encoding (which uses sixty two characters: 0-nine, A-Z, along with a-z) on an integer ID. The ID corresponds on the entry within the database. This method makes sure that the shorter URL is as small as you possibly can.
Random String Era: A different approach should be to generate a random string of a fixed length (e.g., six people) and Look at if it’s already in use within the database. Otherwise, it’s assigned to the lengthy URL.
4. Databases Administration
The databases schema for the URL shortener is usually uncomplicated, with two primary fields:
شركة باركود للتقييم
ID: A singular identifier for every URL entry.
Extended URL: The original URL that should be shortened.
Small URL/Slug: The limited Variation on the URL, normally stored as a unique string.
In addition to these, you should retailer metadata including the creation date, expiration date, and the volume of occasions the limited URL has been accessed.
five. Managing Redirection
Redirection is often a critical A part of the URL shortener's operation. Each time a consumer clicks on a brief URL, the company needs to rapidly retrieve the first URL in the database and redirect the user employing an HTTP 301 (long-lasting redirect) or 302 (temporary redirect) status code.
صورة باركود
Effectiveness is vital right here, as the procedure needs to be nearly instantaneous. Approaches like database indexing and caching (e.g., employing Redis or Memcached) can be utilized to hurry up the retrieval procedure.
6. Safety Criteria
Security is a big concern in URL shorteners:
Destructive URLs: A URL shortener can be abused to unfold destructive links. Employing URL validation, blacklisting, or integrating with 3rd-bash security companies to examine URLs right before shortening them can mitigate this threat.
Spam Prevention: Amount limiting and CAPTCHA can prevent abuse by spammers wanting to crank out Many short URLs.
7. Scalability
Because the URL shortener grows, it may have to manage a lot of URLs and redirect requests. This demands a scalable architecture, maybe involving load balancers, dispersed databases, and microservices.
Load Balancing: Distribute targeted visitors throughout various servers to take care of large loads.
Distributed Databases: Use databases which will scale horizontally, like Cassandra or MongoDB.
Microservices: Different fears like URL shortening, analytics, and redirection into distinctive services to further improve scalability and maintainability.
eight. Analytics
URL shorteners typically give analytics to track how often a brief URL is clicked, wherever the website traffic is coming from, together with other beneficial metrics. This demands logging Each and every redirect and possibly integrating with analytics platforms.
nine. Conclusion
Building a URL shortener will involve a combination of frontend and backend advancement, databases administration, and attention to stability and scalability. Even though it may seem to be an easy service, making a robust, successful, and secure URL shortener offers numerous challenges and calls for cautious setting up and execution. No matter whether you’re making it for private use, internal firm tools, or being a general public provider, understanding the underlying rules and best procedures is important for achievement.
اختصار الروابط
 Amanda Bynes Then & Now!
Amanda Bynes Then & Now! Jonathan Lipnicki Then & Now!
Jonathan Lipnicki Then & Now!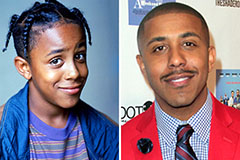 Marques Houston Then & Now!
Marques Houston Then & Now! Erik von Detten Then & Now!
Erik von Detten Then & Now! Melissa Sue Anderson Then & Now!
Melissa Sue Anderson Then & Now!